➤Summary
Telekom Serbia data leak reports surfaced after a threat actor allegedly published sensitive customer information on a cybercrime forum, raising serious concerns about telecom security and personal data exposure. According to forum posts dated March 18, 2026, an individual using the alias Zeus_kos claimed access to internal records originating from scheduler.telekom.rs, an internal scheduling portal. The incident quickly drew attention from cybersecurity researchers and media outlets, highlighting growing risks facing telecom providers worldwide. As organizations increasingly rely on centralized digital systems, breaches involving identity information present long-term consequences beyond immediate financial loss. This spoofguard.io article analyzes what is currently known, how the alleged leak may have occurred, and what companies and users must do to reduce exposure in an evolving threat landscape. 🔐
What Happened: Alleged Leak Overview
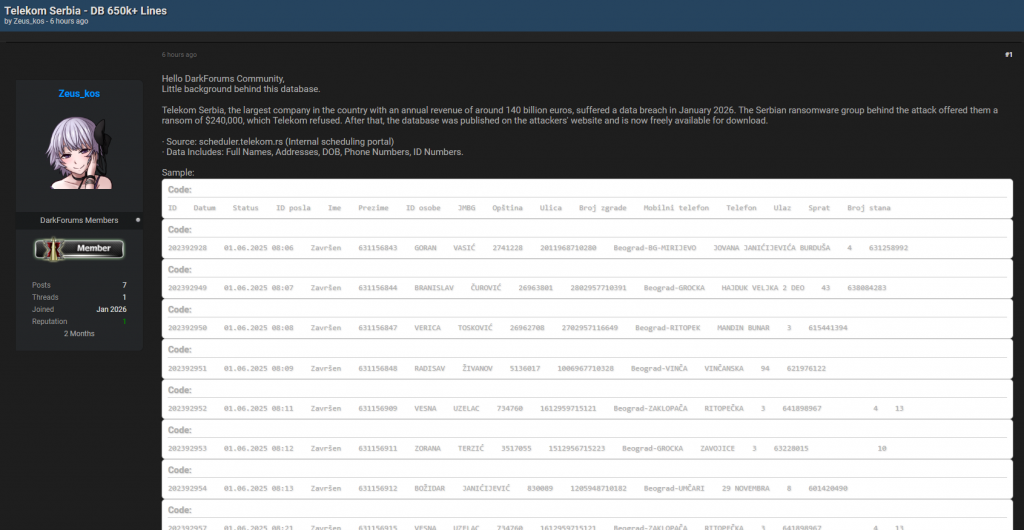
The reported Telekom Serbia data leak originated from the underground forum Darkforums.st, where the attacker claimed possession of customer records. The dataset allegedly includes:
- Full names
- Residential addresses
- Dates of birth
- Phone numbers
- National identification numbers
The attacker stated that the information was extracted from scheduler.telekom.rs, described as an internal operational portal. Shortly after publication, Telekom Serbia responded publicly, saying perpetrators attempted extortion and that investigations were underway. The company emphasized that systems were secured and authorities notified. A detailed media report can be found via n1info.rs.
While verification of the entire dataset remains ongoing, cybersecurity communities treat such claims seriously because telecom databases contain highly sensitive identity intelligence.
Why Telecom Breaches Are High-Impact Events
Telecommunications providers hold massive volumes of personally identifiable information (PII). Unlike passwords that can be reset, identity data remains persistent over time. When exposed, it enables fraud schemes, impersonation attempts, and long-term surveillance risks. 📡
Telecom environments are particularly attractive targets because they connect:
- Customer identities
- Billing systems
- Communication metadata
- Infrastructure access controls
Even partial disclosure may allow attackers to map relationships between individuals and services. This expands the attack surface far beyond the initial breach itself.
Technical Context Behind the Incident
Although full forensic details have not been publicly confirmed, several common attack scenarios align with the claims:
- Credential compromise targeting internal dashboards.
- Misconfigured access permissions.
- API exposure within internal scheduling platforms.
- Insider threat or stolen session tokens.
If the scheduler portal was improperly segmented, attackers could enumerate records without triggering alarms. Modern threat actors increasingly exploit operational tools rather than public websites because they often receive less security scrutiny. 🧠
Security experts frequently warn that internal systems become external risks once credentials are compromised.
Featured Snapshot: Alleged Leak Details
| Category | Information |
| Forum | Darkforums.st |
| Author | Zeus_kos |
| Publication Date | 18 March 2026 |
| Alleged Source | scheduler.telekom.rs |
| Data Type | Customer personal information |
| Company Response | Extortion attempt reported |
| Status | Investigation ongoing |
This structured overview helps analysts quickly evaluate incident severity and response priorities.
Potential Risks for Affected Customers
The Telekom Serbia data leak could expose individuals to multiple threats:
- Identity theft attempts
- SIM-swap fraud
- Targeted phishing campaigns
- Financial scams
- Social engineering attacks
Because telecom identifiers often link to banking authentication systems, attackers may leverage leaked information to bypass verification processes. 🚨
One major concern involves coordinated fraud networks that specialize in combining leaked datasets with publicly available information to create convincing attack narratives.
Question & Answer (Featured Snippet)
Can leaked telecom data be used immediately for fraud?
Yes. Even without passwords, personal identifiers allow attackers to impersonate victims during customer support interactions or verification checks.
The Role of Underground Forums in Data Exposure
Cybercrime forums function as marketplaces for stolen data, proof-of-access posts, and extortion negotiations. Threat actors publish samples to demonstrate authenticity before selling or pressuring organizations.
In this case, the forum publication suggests a strategy designed to increase leverage against the company through public visibility. Analysts note that attackers increasingly rely on reputation systems within underground communities to validate claims before monetization.
Monitoring such spaces has become essential for early breach detection and proactive response planning.
Practical Checklist for Organizations
Use this actionable checklist to reduce exposure risks ✅:
- Implement strict access segmentation for internal portals.
- Enforce multi-factor authentication across operational systems.
- Monitor underground forums for brand mentions.
- Audit privileged accounts regularly.
- Encrypt sensitive databases at rest and in transit.
- Deploy anomaly detection for bulk data access.
- Establish incident response playbooks.
Organizations adopting proactive monitoring frameworks detect threats significantly faster than reactive teams.
Customer Protection Steps After a Data Exposure
Individuals potentially affected by a telecom breach should consider:
- Monitoring account activity closely.
- Enabling two-factor authentication where available.
- Avoiding suspicious calls requesting verification codes.
- Reporting unexpected SIM changes immediately.
- Reviewing credit activity for anomalies.
These steps reduce the probability of successful impersonation attacks following data exposure. 📱
Industry Perspective and Expert Insight
Cybersecurity researchers emphasize that telecom incidents often signal broader ecosystem risks. According to multiple incident analyses, attackers target communication providers because compromising them amplifies downstream attacks across finance, healthcare, and government sectors.
One expert summarized the situation:
“Telecom data breaches rarely stay isolated; they become identity infrastructure attacks.”
This perspective highlights why organizations increasingly rely on digital risk analysts to monitor external threat intelligence signals and emerging leak discussions.
How Organizations Can Strengthen Resilience
Modern security requires more than perimeter defenses. Companies must adopt continuous monitoring and proactive brand defense capabilities. Integrating spoofing prevention solutions helps reduce impersonation campaigns that often follow data leaks.
Broader Cybersecurity Trends Revealed
The Telekom Serbia data leak reflects several evolving industry trends:
- Attackers targeting operational systems instead of public platforms.
- Increased extortion attempts without ransomware deployment.
- Faster publication of alleged datasets on forums.
- Growing reliance on identity-based attacks.
These patterns demonstrate how modern cybercrime prioritizes monetizable personal data rather than infrastructure disruption alone. 🌐
Practical Tip for Security Teams
A key lesson from this incident is visibility. Organizations should monitor not only internal logs but also external threat environments. Early discovery often determines whether an event becomes a crisis or a contained incident.
Security teams should integrate automated intelligence feeds alongside manual investigation workflows to improve detection speed.
Conclusion: Lessons From the Alleged Incident
The Telekom Serbia data leak underscores the growing importance of proactive cybersecurity in telecom infrastructure. Even alleged breaches can trigger widespread concern, reputational risk, and potential fraud exposure. Organizations must prioritize internal system security, continuous monitoring, and rapid incident response to minimize damage when threats emerge.
As cybercriminal ecosystems evolve, transparency and preparedness become critical defenses. Companies that actively monitor external threats and strengthen identity protections are far better positioned to maintain customer trust and operational resilience. 🚀
Discover much more in our complete guide
Request a demo NOW
Disclaimer: SpoofGuard focuses on monitoring and reporting domain spoofing and related online impersonation risks using publicly available threat-intelligence sources. The inclusion or mention of any organization does not imply a confirmed breach, compromise, or wrongdoing.



