➤Summary
The domain threat intelligence community is raising alarms over a newly discovered cyber campaign involving the PowMix botnet, which is actively targeting workers in the Czech Republic. This sophisticated threat leverages stealthy communication techniques, including randomized command-and-control (C2) traffic designed to evade detection. 🔍 By mimicking legitimate API requests, PowMix blends seamlessly into normal network activity, making it especially dangerous for organizations lacking advanced monitoring tools.
According to The Hacker News, the malware embeds encrypted heartbeat data and victim identifiers directly into URL paths, disguising malicious traffic as legitimate REST API calls. This evolution highlights the growing need for phishing domain detection and proactive domain abuse monitoring to identify suspicious infrastructure before it causes harm.
As attackers increasingly rely on domain-based tactics, businesses must rethink their defenses. This spoofguard.io article explores what happened, why it matters, and how organizations can strengthen their protection strategies.
What happened
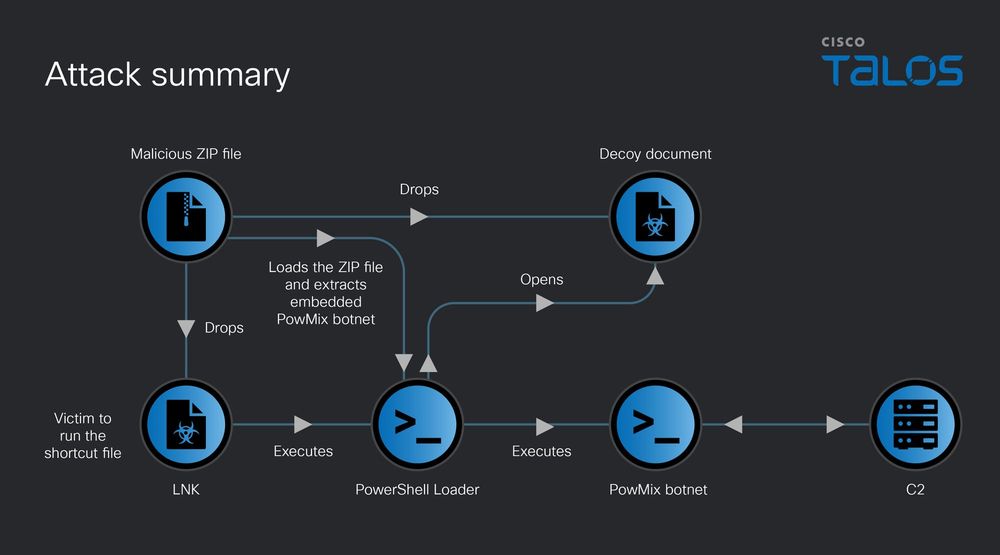
The PowMix botnet represents a new generation of malware that prioritizes stealth and adaptability. It primarily spreads through phishing campaigns targeting Czech employees, tricking them into downloading malicious payloads. 🎯
Once installed, the malware establishes communication with its C2 servers using randomized URL paths that resemble legitimate API endpoints. These URLs contain encrypted data, including unique identifiers for each infected machine. This design makes detection extremely difficult using traditional signature-based tools.
Another critical feature is its ability to dynamically update its C2 domain configuration. This means attackers can switch infrastructure quickly, avoiding takedowns and maintaining persistent control over infected systems.
This behavior underscores the importance of domain threat intelligence, which helps security teams track malicious domains and identify patterns in attacker infrastructure.
Data exposed
Although PowMix is primarily a botnet, its capabilities allow attackers to collect and exfiltrate sensitive data from compromised systems. 💻
Potential data exposure includes:
- Employee login credentials
- Corporate emails and internal communications
- Browser-stored passwords and cookies
- Financial or operational data
Once stolen, this information can be sold or used in further attacks. Cybercriminals often leverage compromised credentials to launch additional phishing campaigns or gain deeper access into corporate networks.
This is where phishing domain detection becomes critical. By identifying malicious domains early, organizations can block communication with attacker-controlled servers before data exfiltration occurs.
Additionally, domain abuse monitoring allows companies to detect suspicious domain registrations that mimic their brand, reducing the risk of impersonation attacks.
Why dangerous
The PowMix botnet is particularly dangerous due to its advanced evasion techniques and scalability. ⚠️
Key risk factors include:
- Use of encrypted and randomized C2 communication
- Ability to mimic legitimate API traffic
- Dynamic updating of C2 domains
- Targeted phishing campaigns
A key question many organizations ask is: Why is randomized C2 traffic so effective?
Answer: Because it blends into normal network behavior, making it difficult for security tools to distinguish between legitimate and malicious traffic.
This level of sophistication means traditional defenses are no longer enough. Organizations must rely on domain threat intelligence to identify suspicious patterns and correlate domain activity with known threat indicators.
Furthermore, attackers can scale this operation globally, expanding beyond Czech workers to target organizations worldwide. 🌍
Without proper domain abuse monitoring, businesses may remain unaware that their brand is being used in phishing campaigns.
Who is at risk
While the current campaign focuses on Czech workers, the techniques used by PowMix can easily be replicated in other regions.
High-risk groups include:
- Enterprises with remote or hybrid workforces
- Organizations lacking advanced email filtering
- Companies without phishing domain detection systems
- Businesses with limited cybersecurity resources
Small and medium-sized enterprises are especially vulnerable. Attackers often exploit weaker defenses to gain initial access before targeting larger networks.
Companies that do not actively invest in domain threat intelligence are at a disadvantage, as they lack visibility into emerging threats and attacker infrastructure.
Additionally, organizations concerned about how to protect brand from phishing must consider the risk of spoofed domains being used to impersonate their services. 🎭
How to prevent
Mitigating the PowMix botnet threat requires a multi-layered approach that combines technology, awareness, and proactive monitoring. 🔐
Security checklist:
- Implement advanced email filtering to block phishing attempts
- Deploy endpoint protection to detect malware behavior
- Use domain threat intelligence tools to monitor suspicious domains
- Enable phishing domain detection to identify malicious infrastructure
- Conduct regular security awareness training for employees
- Monitor DNS traffic for unusual patterns
- Apply domain abuse monitoring to track brand impersonation
A practical tip: regularly audit newly registered domains similar to your brand name. This helps in early detection of spoofed domains used in phishing campaigns.
For organizations asking how to protect brand from phishing, the answer lies in combining proactive monitoring with rapid response strategies.
Expert insight
Cybersecurity analysts emphasize the growing importance of domain-based defenses. As one expert noted, “Attackers are shifting from malware signatures to infrastructure-based evasion. Domains are now the new battlefield.”
This shift highlights the need for continuous monitoring and intelligence gathering. Organizations must adapt quickly to stay ahead of evolving threats.
Conclusion
The PowMix botnet demonstrates how modern cyber threats are becoming more sophisticated and harder to detect. By leveraging randomized C2 traffic and dynamic domain updates, attackers can maintain persistence and evade traditional defenses. 🚀
To stay protected, organizations must adopt a proactive approach centered around domain threat intelligence, phishing domain detection, and domain abuse monitoring. These tools provide the visibility needed to detect threats early and respond effectively.
Businesses that invest in strategies to protect company from spoofed domains will be better equipped to defend against phishing and brand impersonation attacks.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.



