➤Summary
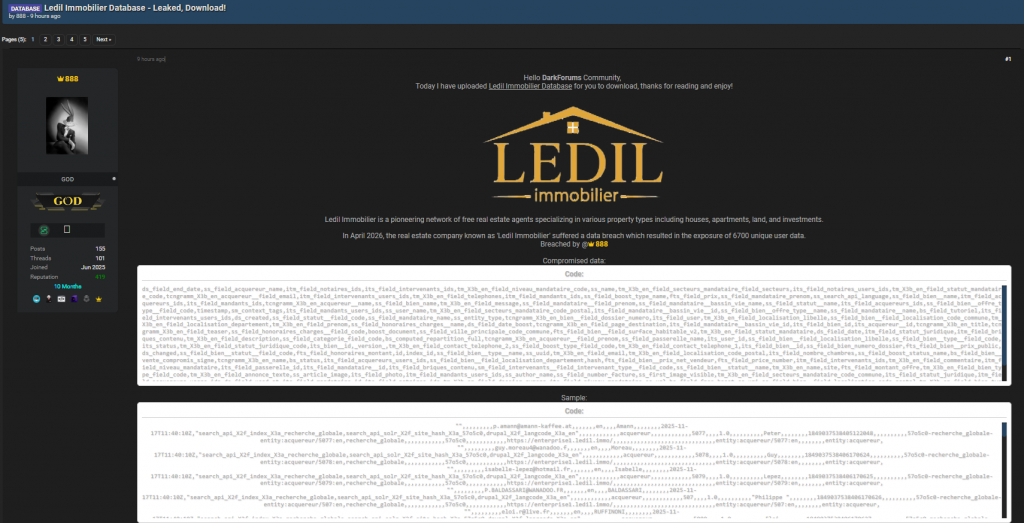
Brand protection has become a strategic priority as cybercriminals increasingly exploit leaked data to impersonate businesses and deceive customers. The alleged database leak involving Ledil Immobilier, reportedly shared on Darkforums by actor “888” on April 22, 2026, highlights how structured business data can be weaponized for fraud and impersonation campaigns.
This exposure includes a large volume of structured fields—ranging from contact data and internal identifiers to property listings and transactional metadata—making it a valuable resource for attackers. For organizations, this incident reinforces the urgent need for domain impersonation detection, brand abuse detection, and proactive monitoring solutions like those offered by SpoofGuard. 🚨
In this guide, we break down how such leaks impact organizations, how attackers leverage them, and how a modern phishing domain monitoring service can help mitigate these risks.
What Happened in the Alleged Ledil Immobilier Leak
The leaked dataset attributed to Ledil Immobilier appears to contain extensive structured records, including:
- Personal identifiers (names, emails, phone numbers)
- Property-related data (pricing, location, transaction status)
- Internal system IDs and user references
- Business workflow metadata (mandates, legal status, notary references)
- Communication fields and messaging content
While the dataset is highly technical, its real danger lies in how easily it can be repurposed for cybercrime. Attackers can reconstruct customer journeys, identify high-value targets, and launch highly convincing scams. ⚠️
Such incidents are increasingly discussed on underground platforms like Darkforums, where threat actors monetize stolen data through resale or direct exploitation.
Why This Matters for Brand Protection
Brand protection is no longer limited to trademark enforcement—it now includes defending against digital impersonation, phishing, and data-driven fraud.
When a dataset like this leak, attackers gain:
- Trusted brand context (logos, communication style)
- Real customer and transaction data
- Internal terminology and workflows
This enables them to create highly convincing fake domains, emails, and websites that mimic legitimate business operations.
💡 Key insight: The more detailed the data leak, the more credible the impersonation attack becomes.
Organizations that fail to invest in brand abuse detection risk losing customer trust and facing financial and reputational damage.
How Attackers Exploit Leaked Business Data
Once exposed, structured datasets become tools for multiple attack vectors:
- Phishing campaigns: Personalized emails referencing real transactions
- Domain spoofing: Creating lookalike domains to trick users
- Invoice fraud: Sending fake payment requests using real data
- Account takeover: Leveraging exposed emails and identifiers
For example, attackers can use fields like pricing, property details, and contact names to craft emails that appear completely legitimate.
This is where domain impersonation detection becomes critical—it helps identify fraudulent domains before they are widely used in attacks. 🔍
Business Risks and Impact
The consequences of such a leak extend far beyond the initial exposure:
- Customer trust erosion: Clients may fall victim to scams
- Financial losses: Fraudulent transactions and reimbursements
- Legal exposure: GDPR and compliance violations
- Operational disruption: Incident response and recovery efforts
- Brand damage: Long-term reputation decline
Organizations in sectors like real estate are particularly vulnerable due to the high-value transactions involved.
Without effective brand protection, companies risk becoming targets for ongoing impersonation campaigns. 🏢
Detection and Prevention Strategies
To mitigate risks, organizations must adopt a proactive security approach:
- Deploy a phishing domain monitoring service
- Implement domain impersonation detection tools
- Use automated alerts for suspicious domain registrations
- Monitor dark web forums for leaked data
- Enforce email authentication protocols (DMARC, SPF, DKIM)
Solutions like SpoofGuard provide advanced brand abuse detection capabilities, helping organizations identify and neutralize threats early.
Practical Checklist for Immediate Action ✅
- Audit exposed data and identify affected users
- Monitor newly registered domains مشابه to your brand
- Enable multi-factor authentication (MFA)
- Educate customers about phishing risks
- Establish an incident response plan
- Use an automated domain takedown service to remove malicious sites quickly
These steps significantly reduce the attack surface and improve resilience against impersonation threats. 🛡️
Real-World Use Case: From Data Leak to Phishing Attack
Imagine an attacker using the leaked Ledil dataset:
- Extracts customer names and property details
- Registers a lookalike domain similar to the company
- Sends emails referencing real transactions
- Requests payment to a fraudulent account
This type of attack is highly effective because it combines real data with brand impersonation.
Question: Why are data-driven phishing attacks more dangerous?
Answer: Because they use real information, making them far more convincing and harder to detect.
The Role of Brand Abuse Detection in Modern Security
Brand abuse detection plays a crucial role in identifying threats across digital channels, including:
- Fake websites and domains
- Social media impersonation
- Fraudulent email campaigns
- Unauthorized use of brand assets
When combined with brand protection strategies, it creates a comprehensive defense system against evolving cyber threats. 🔐
Conclusion: Strengthening Your Brand Defense Strategy
The alleged Ledil Immobilier leak is a clear example of how structured business data can fuel sophisticated cyberattacks. Organizations must move beyond reactive security and adopt proactive measures such as brand protection, domain impersonation detection, and continuous monitoring.
By leveraging advanced tools like SpoofGuard, businesses can detect threats early, protect their customers, and maintain trust in an increasingly hostile digital landscape. 🚀
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.



